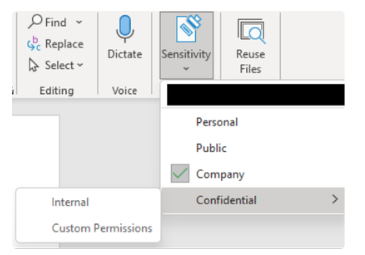
The good news is that Microsoft is providing solutions for this, too. A first step towards better security is to manually add sensitivity labels to documents. The main function of these labels within Microsoft 365 is to indicate what type of content a document contains. If the content is confidential, then you as the document manager can add an encryption layer to it, ensuring that only authorized parties with the correct key have access to the encrypted document. Unauthorized parties who accidentally receive the same document can’t open, read or edit it. What’s more, everything that happens with that document after labeling is also systematically tracked in your compliance policy. This way, you can extend access to that document afterwards, revoke it again, limit it in time – you name it."
Second step: automatic labeling
When it comes to security, manual work is far from ideal, especially if that work is done by end users. After all, people remain the weakest link in security. “That’s why it’s better to automate labeling,” says Rotthier.
"You can do that by using Defender for Cloud Apps. That’s Microsoft’s Cloud Access Security Broker, CASB for short. The tool works on the basis of classifiers that can recognize typical, recurring content in documents: from address to passport details, and from bank account to credit card numbers. Based on that content and the policies you set and combine, documents are then automatically classified. To top it all off, Microsoft also provides trainable classifiers. You can teach them to recognize specific content from your company, create a label based on that, and automatically apply that label to certain documents as well."
Third step: classify
“Employees who have access to such a label must also be able to change it,” continues Rotthier. "For example, information may no longer need to remain confidential. Then you need to be able to lower the classification of that document to make it more accessible. In doing so, I advise customers not to use more than ten labels. Otherwise, it will just become one big jumble.
If you raise a label from a lower to a higher classification, it can happen automatically. However, if you go from a higher to a lower classification, you’ll also have to enter a justification for it. Of course, the system keeps track of who has changed a label classification."
Customizing
“Unfortunately, when it comes to data privacy governance, there’s no one-size-fits-all solution,” Rotthier concludes. "A lot depends on the type of business you are and the industry you operate in. So it certainly doesn't hurt to seek specialized outside help with that."
Want to learn more?
Are you in control of your data in M365? Do the right users have access to all the items they need? In a world where data breaches are making the news every day and Teams continues to grow, these questions are more relevant than ever. That is why it is so important to define your security priorities. What breaches do you want to avoid at all costs? Which technologies do you use and what initiatives are you planning? Through our Priority Assessment, our experts will help you get started and give you an insight into potential minor adjustments to your existing environment that will have a major impact on the security level. For more information about this, don’t hesitate to contact your trusted Inetum-Realdolmen contact person, our experts or send an email to info@inetum-realdolmen.world .

 There is no shortage of data privacy regulations. All you have to do is implement all these rules within your organization. “Fortunately, technology such as Microsoft 365 offers plenty of opportunities to successfully meet this complex challenge,” says colleague Joeri Rotthier, who specializes in M365 security as a technical consultant.
There is no shortage of data privacy regulations. All you have to do is implement all these rules within your organization. “Fortunately, technology such as Microsoft 365 offers plenty of opportunities to successfully meet this complex challenge,” says colleague Joeri Rotthier, who specializes in M365 security as a technical consultant.